ASRG webinar on CAN protocol attacks
I recently gave a 45 minute webinar at the ASRG on the topic of CAN protocol attacks, demonstrating five different attacks on the CAN protocol itself. There is also a PDF version (22MB) of the slides.
The demonstration used the CANHack toolkit running on a Canis Labs CANHack board, attacking two CANPico boards. We use the CANHack board for training courses but don’t sell it because the CANPico board can be started in CANHack mode (the boards have GPIO access to the CAN transceiver). The MicroPython SDK manual in the ‘docs’ folder of the CANHack GitHub repo explains how to put the board into this mode. CANPico boards are available via our distributor SK Pang.
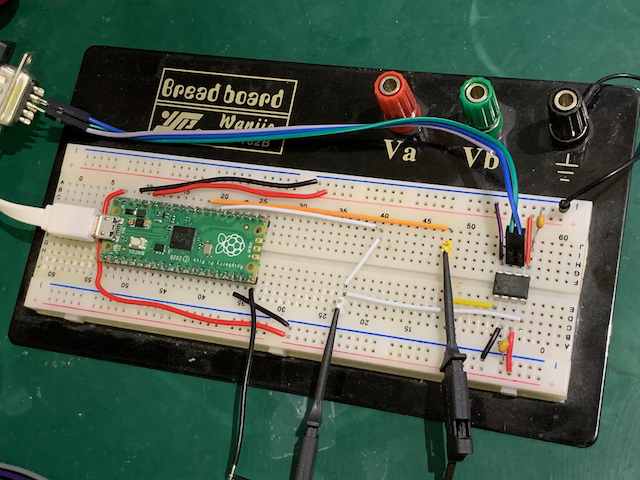
It’s also pretty straightforward to make your own CANHack board using breadboard and a CAN transceiver.