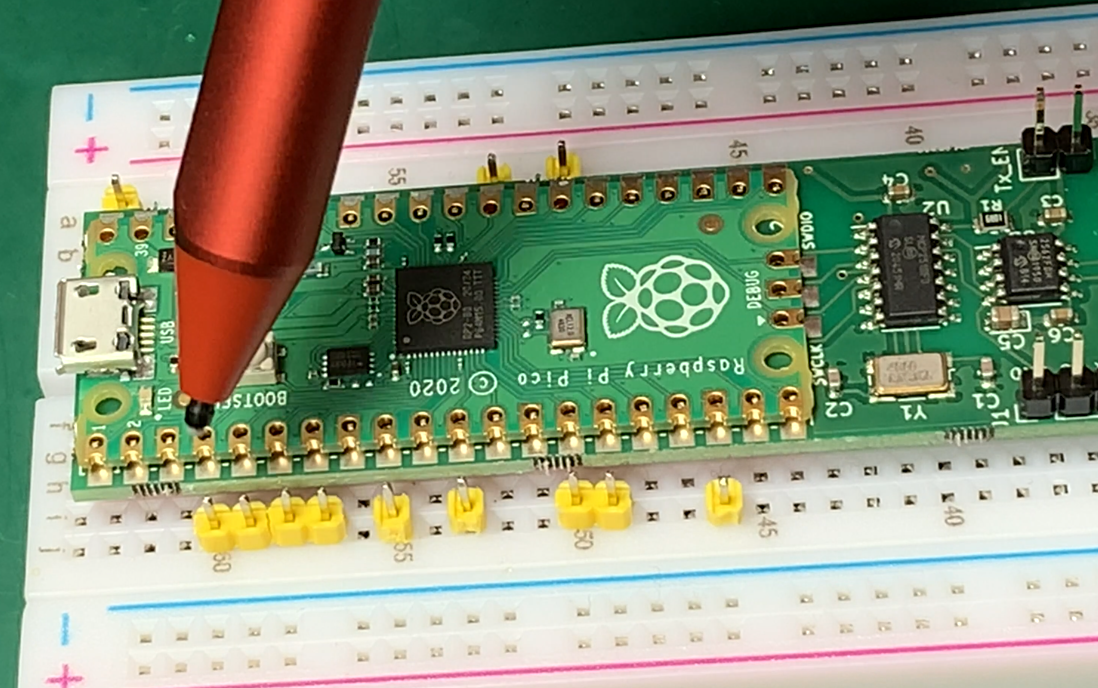
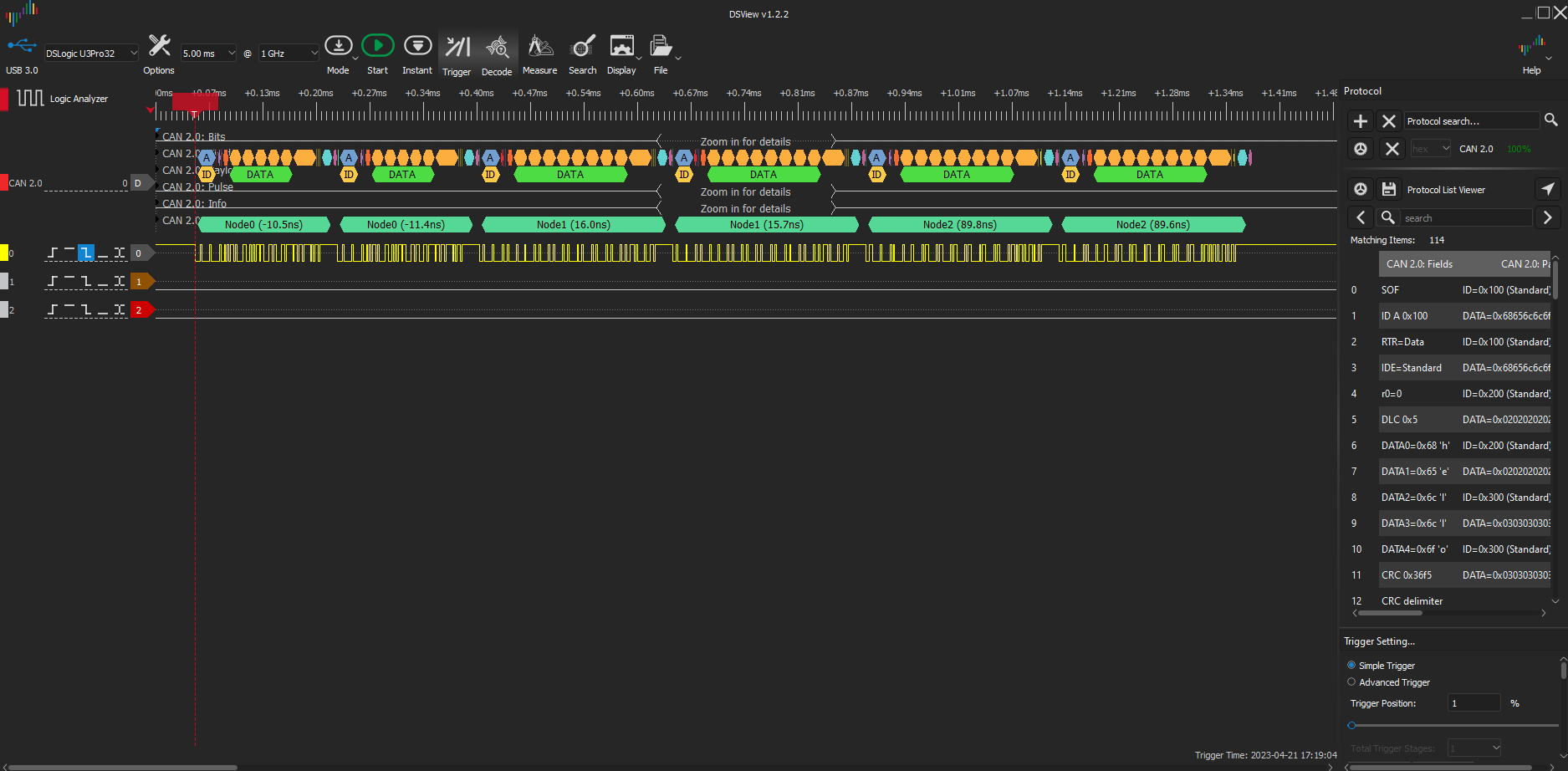
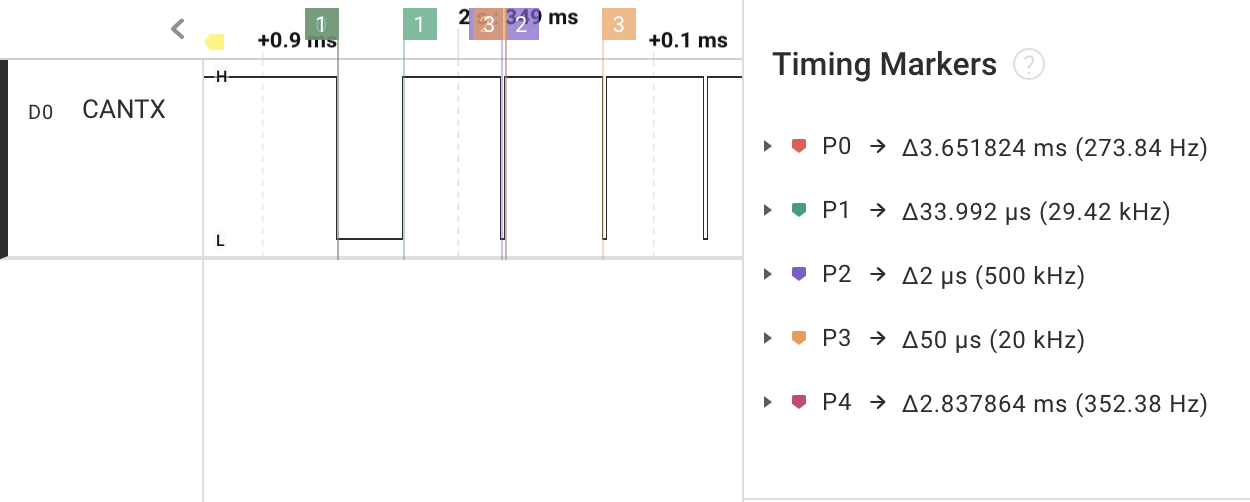
Welcome to the blog of Dr. Ken Tindell, CTO of Canis Automotive Labs. This blog is focused on the work Canis is doing on CAN bus and CAN security, but also covers the design of embedded software and hardware for automotive systems and the Yes We Can project at Canis that develops hardware, software and tools for CAN bus: the CANHack toolkit for injecting faults into the CAN protocol, CANPico and CANHack hardware boards for the Raspberry Pi Pico, and the can2 logic analyzer CAN protocol decoder.